Consider this an evergreen article with *pro-active adds/moves/changes inclusive of errors/mistakes until I remove this statement.
The following content is a brief and unofficial prerequisites guide to setup, configure and test delivering Microsoft teams within a Citrix virtual desktop powered by Citrix Virtual Apps & Desktops (CVAD) Service – https://docs.citrix.com/en-us/citrix-virtual-apps-desktops-service.html in Citrix Cloud prior to deploying in a PoC, Pilot or Production environment. The views, opinions and concepts expressed here are those by the author only and do not necessarily conform to industry descriptions nor leading practises. The views expressed here are my own and do not necessarily reflect the views of Citrix.
Shortened Names
SKYPE FOR BUSINESS – skype4b
CITRIX VIRTUAL DESKTOP – cvd
CITRIX VIRTUAL APP & DESKTOP – cvad
VIRTUAL DELIVERY AGENT – vda
HIGH DEFINITION EXPERIENCE – hdx
VIRTUAL DESKTOP – vd
VIRTUAL APPS – va
REALTIME MEDIA ENGINE – rtme
CITRIX WORKSPACE APP – cwa
MICROSOFT TEAMS – teams
CURRENT RELEASE – cr
LONG TERM SERVICE RELEASE – ltsr
Very Importantly Notice*
“This feature depends on a future Microsoft Teams release. We will update this description as information about the version and release date become available.” referenced directly from – https://docs.citrix.com/en-us/citrix-virtual-apps-desktops/multimedia/opt-ms-teams.html#system-requirements.
Introduction
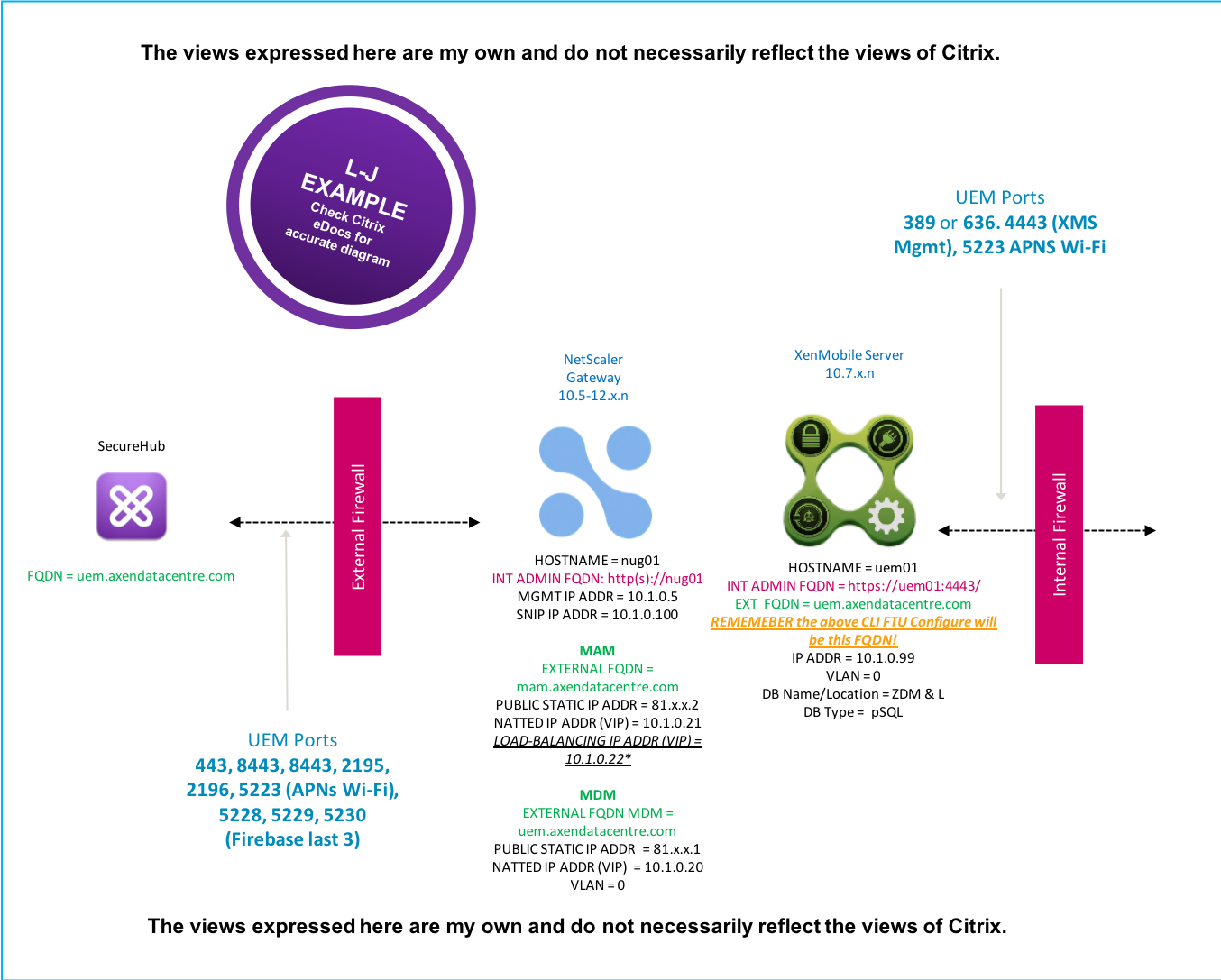
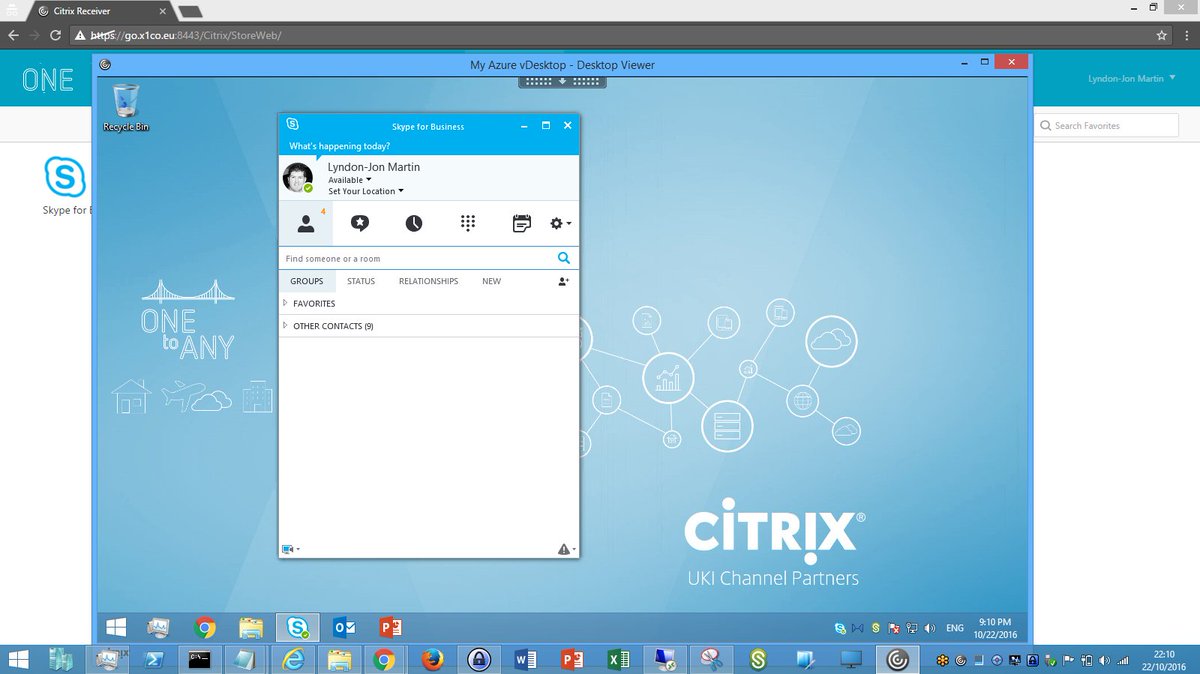
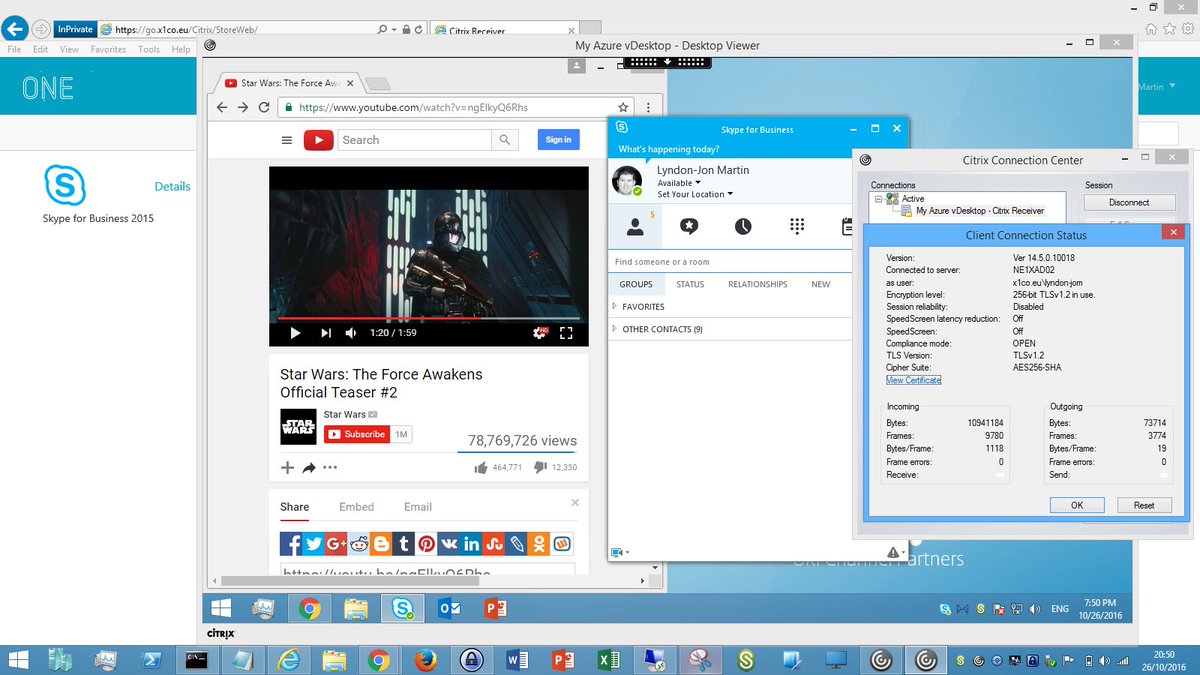
In May 2016 I published the following blog post entitled “Deploying Skype for Business 2015-16 (Offloaded) from a Citrix HDX Optimised Virtual App or Desktop” available at – https://axendatacentre.com/blog/2016/04/25/deploying-skype4b-2015-offloaded-from-a-citrix-hdx-virtual-app-or-desktop/. Suggested before you continue reading this post please read the “Optimization for Microsoft Teams” documentation on Citrix eDoc’s at – https://docs.citrix.com/en-us/citrix-virtual-apps-desktops/multimedia/opt-ms-teams.html or study if you are pressed for time the below architecture diagram for ease of use, of the joint Citrix + Microsoft solution to offload the audio/video processing of Teams from a Citrix Virtual Desktop to the employees local endpoint that is required to run a supported OS + Citrix Workspace app + Real-Time Media Engine (RTME). I still encourage you to please read the documentation in full prior to continuing reading.
Check out the Architecture for the HDX Offloading for #Teams with @Citrix – https://t.co/iUxrG9l8M4 – Optimization for Microsoft Teams p.s please read the NOTE at the top of the document article. pic.twitter.com/PXq0mYaitI
— Lyndon-Jon Martin 👨🏻💻 (@lyndonjonmartin) August 6, 2019
It is also worth understanding Microsofts basic architecture overview of the solution which is available at – https://docs.microsoft.com/en-us/microsoftteams/teams-for-vdi#teams-on-vdi-with-calling-and-meetings.
The Employee Experiences with Teams HDX Offloaded
Windows
Linux (x64 Linux distributions only)
Understanding a HDX Optimised vs. Non-Optimised CVAD Deployment
The following HTML diagram depicts the differences between (un)optimised, I’ve also included a few suggested considerations as well.
| Non-Optimised | Optimised for HDX Teams Offloading | ||||||||||||||||||||||||||||||
|
|
||||||||||||||||||||||||||||||
1. It’s very important to recognise that employees will find themselves in a situation where the connected end-point is unoptimised during work from home scenario e.g COVID-19 and therefore you should plan for these scenarios by implementing the right vs. relevant HDX policy strategy “Balanced” vs. “Preferred” see below guidance.
2. Educate employees when using a non corporate device e.g personal device at home during to COVID-19 they will likely be consuming an un-optimised version of Teams in CVAD, its important to set a exception to avoid unnecessary help desk tickets/calls.
3. Any and all exchanged IM’s and documents live within the CVAD lens meaning that your IP + Pii in any documents lives within the employees CVAD resource e.g Virtual Desktops when they exported it from a IM’s vs. channel(s) in Teams. It is also important to recognise that those same IMs’ vs. channel(s) originate and are available in Microsoft Teams on any device as the source, so if employees re-frame teams outside of your Citrix virtual desktop your IP + Pii in documents could be exfiltrated if the employee device(s) are not properly managed by IT e.g MEM, UEM, MAM, Secure SaaS check out – https://www.mycugc.org/blogs/lyndon-jon-martin/2020/03/27/secure-saas-on-zero-trusted-vs-earned-trusted-devi for more information.
LTSR vs. CR Strategy for HDX Offloading of Microsoft Teams?
It’s worth understanding that if your CVAD deployment strategy is to use the Long Term Service Release (LTSR) then you will not receive any new features only bug fixes this thinking keeps inline with the current CVAD strategy between CR vs. LTSR (stability and long-term – https://docs.citrix.com/en-us/citrix-virtual-apps-desktops/1912-ltsr.html) release cycles. Consuming a CR branch means that you can unlock new features as they become available by upgrading your CVAD on-premises of upgrade the CVAD Service components within your Resource Locations (RL).
| Release Strategy | New Features | Bug Fixes | Documentation |
|---|---|---|---|
| CVAD Service | |||
| On-premises Current Release (CR) | https://docs.citrix.com/en-us/citrix-virtual-apps-desktops/multimedia/opt-ms-teams.html | ||
| Long Term Service Release (LTSR) | https://docs.citrix.com/en-us/citrix-virtual-apps-desktops/1912-ltsr/multimedia/opt-ms-teams.html |
Pre-requisites & System Requirements Key Highlights Only
The full and complete list is available at – https://docs.citrix.com/en-us/citrix-virtual-apps-desktops/multimedia/opt-ms-teams.html*, there is also a Citrix TechZone article published at – https://docs.citrix.com/en-us/tech-zone/design/reference-architectures/optimizing-unified-communications-solutions.html. The below are the key highlights that should be focused on to be successful.
1. You will require the following MSFT teams version “1.2.00.31357” in order to be able to take advantage off the HDX Offloading capabilities within a supported CVAD environment. The following Citrix Workspace app (CWa) versions are the suggested vs. minimal versions that will be required to HDX offload Teams A/V traffic onto the employees endpoint:
Windows
Minimum Version: Citrix Workspace app 1911 for Windows
Download (1911): https://www.citrix.com/en-gb/downloads/workspace-app/legacy-workspace-app-for-windows/workspace-app-for-windows-1911.html
PDF Documentation (1911): https://docs.citrix.com/en-us/citrix-workspace-app-for-windows/1911/citrix-workspace-app-for-windows-1911.pdf
Linux
Minimum Version: Citrix Workspace app 2006 for Linux running on x64 Linux distributions.
Download (2006): https://www.citrix.com/en-gb/downloads/workspace-app/linux/workspace-app-for-linux-latest.html
PDF Documentation (CR): https://docs.citrix.com/en-us/citrix-workspace-app-for-linux/citrix-workspace-app-for-linux.pdf
Mac – Technology Preview
Technology Preview Version: Citrix Workspace app 2009 for Mac OSX running on 10.15.
Download (2009): https://www.citrix.com/en-in/downloads/workspace-app/betas-and-tech-previews/workspace-app-tp-for-mac.html
Provide Feedback https://podio.com/webforms/22969502/1632225
2. Avoid using the .exe installer for Teams – https://docs.citrix.com/en-us/citrix-virtual-apps-desktops/multimedia/opt-ms-teams.html#microsoft-teams-installation.
3.The Citrix HDX Teams policy “Microsoft Teams redirection” – https://docs.citrix.com/en-us/citrix-virtual-apps-desktops/policies/reference/ica-policy-settings/multimedia-policy-settings.html#microsoft-teams-redirection, is ON by default as per https://docs.citrix.com/en-us/citrix-virtual-apps-desktops/multimedia/opt-ms-teams.html#microsoft-teams-installation.
4.CTXMTOP is a Citrix HDX virtual channel used for command and control purposes and no media is therefore exchanged between the CWa running on the end-point and the VDA running in the resource location (data centre).
5. In terms of network connectivity requirements PLEASE NOTE that MSFT Teams utilises Media Processor servers in Office 365 for meetings which affects the behaviour of two peers in point-to-point call scenarios, you can learn more at – https://docs.citrix.com/en-us/citrix-virtual-apps-desktops/multimedia/opt-ms-teams.html#network-requirements, you should be thinking about near to local breakout from end-points to ensure IP transmits to Office365 over the most efficient and faster available route to avoid any/all employee experience degradation this will also directly apply to any MSFT teams clients on native devices that aren’t HDX Offloaded so take note! If you are a Citrix SD-WAN customer take a look at – https://docs.citrix.com/en-us/citrix-virtual-apps-desktops/multimedia/opt-ms-teams.html#citrix-sd-wan-optimized-network-connectivity-for-microsoft-teams likewise if you are not a Citrix SD-WAN customer please take the opportunity to understand why you need to be thinking about an SD-WAN solution for your modern workplace.
6. You will need to update your Windows Firewall ACL on Windows endpoints to avoid the offloading failing by allowing “HdxTeams.exe (HDX Overlay Teams)“, you learn more at – https://docs.citrix.com/en-us/citrix-virtual-apps-desktops/multimedia/opt-ms-teams.html#firewall-considerations.
7. Understanding Screen sharing – https://docs.citrix.com/en-us/citrix-virtual-apps-desktops/multimedia/opt-ms-teams.html#screen-sharing-in-microsoft-teams.
Deploying HDX Offloading (HDX Optimisation Pack ) for Microsoft Teams in a Citrix Virtual App vs. Virtual Desktop
1.The minimum on-premises control plane required is 1906 running the 1906.2 VDA reference – https://docs.citrix.com/en-us/citrix-virtual-apps-desktops/multimedia/opt-ms-teams.html#system-requirements and
2.You need to enable the following policy in Studio for 1906 see page at 668 – https://docs.citrix.com/en-us/citrix-virtual-apps-desktops/downloads/citrix-virtual-apps-and-desktops-1906.pdf to enable “Microsoft Teams redirection” which is also documented at – https://docs.citrix.com/en-us/citrix-virtual-apps-desktops/multimedia/opt-ms-teams.html#system-requirements.
3.Endpoints should be running Citrix Workspace app for Windows 1907 but the recommended version is 1909 and be sure to configure the Windows ACL for Windows Defender Firewall to allow the “HDX Overlay Teams” app to traverse the right vs. relevant networks for more information please check out – https://docs.citrix.com/en-us/citrix-virtual-apps-desktops/multimedia/opt-ms-teams.html#firewall-considerations.
4. The Citrix TechZone micro-site includes few detailed Proof of Concept web document at – https://docs.citrix.com/en-us/tech-zone/learn/poc-guides/microsoft-teams-optimizations.html#policy-settings entitled “Proof of Concept guide for Microsoft Teams optimization in Citrix Virtual Apps and Desktops environments” to help you setup, configure and deploy Microsoft Teams through a CVAD session or lens. It is a must read and therefore I have chosen to not repeat of any of the authors great work expect what was in my original post 06/08/2019. A fellow Citrix colleague Wendy Gay, published a simple guided step by step overview at – https://citrixie.com/2020/04/14/installing-teams-optimization-pack/ which is worth reading.
Microsoft Teams Leading Deployment Practises for Teams in Citrix VDI
1. Migrate Teams on VDI with chat and collaboration to Citrix with calling and meetings – https://docs.microsoft.com/en-us/microsoftteams/teams-for-vdi#migrate-teams-on-vdi-with-chat-and-collaboration-to-citrix-with-calling-and-meetings.
2. Teams on VDI performance considerations – https://docs.microsoft.com/en-us/microsoftteams/teams-for-vdi#teams-on-vdi-performance-considerations.
3. Known issues and limitations – https://docs.microsoft.com/en-us/microsoftteams/teams-for-vdi#known-issues-and-limitations
CWa Endpoint Update Release Strategy
It is important to recognise that you will need to manage the versions of supported CWa out in the field to avoid the HDX Offloading of Teams breaking and causing a degraded employee experience reverting to fallback of A/V. Please note that each supported OS platform has a different management strategy. You should also please take into account Microsofts recommendations – https://docs.microsoft.com/en-us/microsoftteams/teams-for-vdi#install-or-update-the-teams-desktop-app-on-vdi.
| Platform | Manual | Automatic | IT Controlled | Link |
|---|---|---|---|---|
| Windows | https://docs.citrix.com/en-us/citrix-workspace-app-for-windows/update.html#advanced-configuration-for-automatic-updates-citrix-workspace-updates | |||
| Linux | https://docs.citrix.com/en-us/citrix-workspace-app-for-linux/install.html#update |
Tech Insight – Microsoft Teams Optimization with Citrix
This video provides a detailed guided overview of the joint architecture, employee experience, optimisations inclusive of using Citrix SD-WAN, teams call routing and more. Originally posted to the Citrix TechZone at – https://docs.citrix.com/en-us/tech-zone/learn/tech-insights/microsoft-teams-optimization.html.
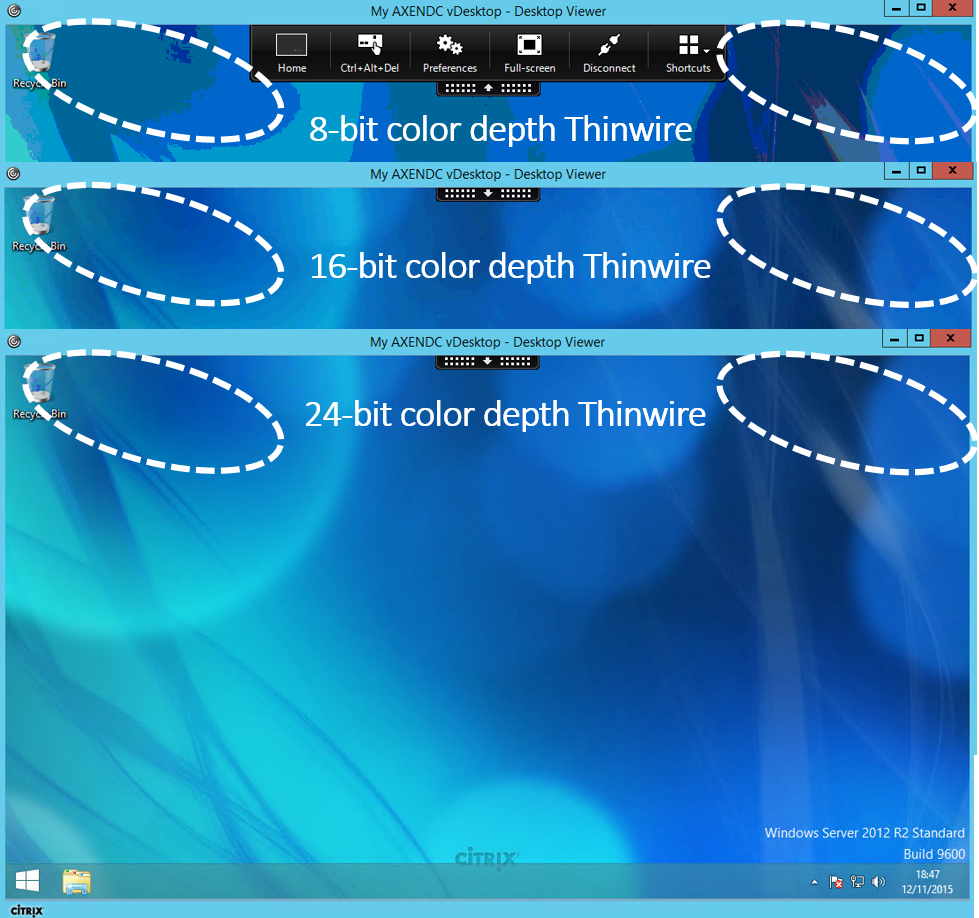
Suggested HDX Broadcast (Remote Graphics Mode) Policy for 7.15 Long Term Service Release (LTSR)
*Please be aware that Citrix eDocs is very clear when it states that Citrix does NOT support Teams HDX Offloading Optimisation for 7.15 Long Term Service Release (LTSR) as it is NOT listed as a supported CVAD platform, you still may wish however to test Microsoft Teams operationally e.g test out its impact on compute, I/O, user profile e.t.c and then purely for fallback failures aka NO HDX Offloading Optimisation BUT you will not be able to test the employee experience of HDX Offloading the audio/video traffic as it is NOT supported remember*). You’ll make use of your UAT 7.15 LTSR environment to be ready for a 2020-21 deployment on a supported CVAD release that supports HDX Offloading for Microsoft Teams, therefore use the built-in default HDX policy “Use video codec for compression” selecting “Use video codec when preferred” which means the following “This is the default setting. No additional configuration is required. Keeping this setting as the default ensures that Thinwire is selected for all Citrix connections, and is optimized for scalability, bandwidth, and superior image quality for typical desktop workloads.” reference the 7.15 LTSR documentation at – https://docs.citrix.com/en-us/xenapp-and-xendesktop/7-15-ltsr/graphics/thinwire.html which will probably be ok for testing under the current release that you are consuming. Final Remember: CVAD formerly XAD 7.15 LTSR platform is NOT supported for Teams Optimisation. TIP: Definitions can change between CR vs. LTSR within the HDX stack which is consistently improving and being updated to offer better employee experiences all the time e.g introduction of net new H.264 standards so always be sure to check the differences between CR vs. LTSR and CR vs. CR versions.
Transitioning from Skype for Business to Teams
A number of few folks have asked the question can I mix and match Skype for Business and the Teams Optimisation Packs together? Its actually a complex answer but the immediate answer as of 03/08/2019 is below, BUT always be sure to circle back and review Citrix’s documentation for the latest supporting statements and interoperability at – https://docs.citrix.com around Teams Optimisation and when searching use “Teams Optimization”. Tip use American spelling for better results.
We only support windows CWA at the moment, which can coexist with RTME. A Mac CWA will be simply not load Teams in optimized VDI mode so we fall back to server side rendering.
— Fernando Klurfan (@CitrixFerK) August 3, 2019
The response is complex and is as follows, answers received vary dependant upon your role Citrix vs. Skpye4B/Teams SysAdmin or Consultant. As I work at Citrix today (Aug 2019) lets focus on a Citrix based role to Teams response:
1. Complete LOB app readiness of Teams including new HDX services/API’s to enable HDX Offloading within a the master image but hidden + unavailable using techniques like disabling the services for each (whatever you prefer), Citrix app layering, MSFT app masking e.t.c. TIP: Pay attention to understand the compute utilisation differences between Teams vs. Skype4B there is a difference.
2. I still need to push out the required RTME to all employee end-points so I don’t want to break the employee experience while we transition to Teams. It is expected to have backwards compatible within Citrix Workspace app for older Virtual Delivery Agent (VDA) versions check eDocs for the backwards compatibility.
3. I only want to transition employees by AD or Citrix Delivery group (department, trusted test groups e.t.c) to Teams based upon point 2 and perform a staggered canary rollout like Citrix Cloud does for each of its services.
4. The person(s) within the Skype for Business/Teams based role(s) need to setup/conf and then test the audio/video codecs prior to enabling Teams at a company wide scale, for me personally this point is actually the most critical because as you offloading the audio/video to the end-point when using HDX Offloading the back-end compute + network resources low aka aren’t taken any much of a real hit HOWEVER if the HDX Offloading fails then you really, really need to understand the impact of processing of the A/V within the Citrix session and what affect it will have on the employees experience so when he/she is completed there final tests, you should prior to a final rollout perform a test side by side two identical end-points one optimised and the other un-optimised and be sure to capture the compute + network requirements client and server side, including the network traffic and score the experience out of 10 for voice and video, the test should be done with wired (where possible today), wireless (Wi-Fi) and 4G internet connectivity in two separate locations an Office (think QoS) and at home (no QoS).
5. Once you have the results from point 4 you may want to re-evaluate your existing HDX Broadcast policies (remote graphics mode e.t.c) and take into account a fall-back scenario if HDX Offloading fails whatever the reason, you may also prefer to leave it as is, however I would strongly suggest creating an emergency fallback HDX Broadcast policy stack but it should be DISABLED and only manually pushed out only if required. The fallback HDX Broadcast policy stack is to preserve the employee experience as best you can if something goes wrong and when I mean something goes wrong I mean a non-Citrix update breaks the optimisation somehow as in reality the Citrix components e.g VDA, HDX Services/API, RTME and Citrix Workspace app are less likely to change within a 12 month period.
6. Citrix’s CR documentation for CVAD is updated to include a digram and overview of “Microsoft Teams and Skype for Business Coexistance” – https://docs.citrix.com/en-us/citrix-virtual-apps-desktops/multimedia/opt-ms-teams.html#microsoft-teams-and-skype-for-business-coexistance.
Managing Employee Experience when Teams HDX Offloading is NOT available
Most folks are not aware that you can control what happens when Microsoft Teams is NOT been HDX offloaded also referred to as Optimised in a Citrix Virtual Apps & Desktops session. You can achieve or rather control the following when “Fallback Mode” occurs either when a the employees connects from an unsupported endpoint + CWa version e.g CWa for HTML5 or they switch from a IT managed endpoint to a BYO endpoint with the incorrect CWa installed (older and unsupported) or IT has not updated the VDA stack within the master image within the Citrix Cloud Resource Location or preferred cloud data centre type.
You can when the optimisation is unavailable enforce no fallback or audio only (suggested and preferred), if you don’t set either of these options the default is to fallback to allowing the Citrix ICA/HDX protocol to do what it does best optimises the remoted session, you can learn more at – https://docs.citrix.com/en-us/citrix-virtual-apps-desktops/multimedia/opt-ms-teams.html#peripherals-in-microsoft-teams.
Suggested “Balanced” HDX Broadcast (Remote Graphics Mode) Policy for Fallback
In 2016 I proposed the following HDX policy for remote graphics “Use video codec for compression” to be set to “For actively changing regions” to preserve the employee experience in a fallback scenario, its now 2019 and my Suggested HDX policy remains unchanged as long as the key goal is to preserve the employee experience to meet that HD experience and it will come at a back-end compute + network traffic spike, including increased network traffic between server and client to process the video H.264/H.265 streams.
Once upon a time I was a SysAdmin and still am at my core so I’ll have an emergency HDX policy in place BUT disabled I call it “HDX Adaptive Display v2 (Balanced)” you configure it as follows selecting the following HDX policies in Studio:
1.”Use video codec for compression” then select “For actively changing regions“
2. “Preferred color depth for simple graphics” then select “16 bits per pixel” and also try 24.
3. Select “Frames Per Second” and select the target FPS to circa 25 from the default which is 30.
NEW 11/10/2019 you could look to utilise “Progressive Mode” – https://docs.citrix.com/en-us/citrix-virtual-apps-desktops/graphics/thinwire.html#progressive-mode, I have not tested this myself yet however it may work for your organisation if you already have it in-place actively.
I wrote a myCUGC article entitled “HDX Leading Best Practices for your Modern Secure Workspace” at – https://www.mycugc.org/blogs/cugc-blogs/2017/09/15/hdx-leading-best-practices-for-your-modern-secure which has some interesting thoughts and insights from nearly 2 years ago which you may find useful and yes I will write an updated article this year time permitting to complete my testing which requires extensive field testing with different devices I don’t just use a lab + network at home, I base 95% of all my article suggestions of what/how to configure settings vs. practises from my personal lab hosted in AWS EC2 in N.Virginia to delivered to end-points in the City of and Greater London, England so its not definitely poppy cop its real world + life scenarios and use cases that I test.
Suggested “Preferred” HDX Broadcast/RealTime/MediaStream (Remote Graphics Mode, Audio and Video) Policy inclusive of Fallback
YES I am contradicting the above suggested HDX Broadcast fallback policy, which I have now renamed to “Balanced” from my initial post and why it still remains is that it will support organisations of any size vs. scale vs. deployment rollout vs. connected devices supporting a balance between video, audio and the remoted display so when an outage occurs and neither I nor will you know what its going to be impacted for example it could be 1x MPLS circuit failure (tip check out Citrix SD-WAN link bonding demo from Jan 2016 vs. case study vs. product page) vs. degradation of all internet circuits due to bad BGP route injections, you get the idea. I’m cautious being an ex-SysAdmin/Consultant and therefore I will summary the key differentiators from my own perspectives as follows in order:
1. How important is the employee experience? For me personally this is always #1 as today’s 2019 reality, employees want an HD 4K experience consistently therefore my personal advise is utilise the built-in default HDX policies within the Current Release (CR) typically minus 2/3 of current CVAD release with your desired HDX employee experience policy tweaks.
2. Once you understand how the humans (employees) within your organisation work using Skype for Business vs. Teams you will have better context as to the WHAT should be in your fallback policy for DR, business continuity or just individual employee devices going into fallback mode. For example understanding your employees is key lets take a look at a practical example by industry vertical, a call centre employee is more interested in better audio quality with customers vs. a clinician on a video call discussing a patients surgical/recovery plan looking at patient records.
3. Re-evaluate once every 3-4 months by asking, polling quick surveys and looking at the metrics made available in both Skype for Business vs. Teams as lets be honest its not a light switch its a journey from one to the other.
Now that you understand your humans (employees) keeping point 3 in mind and begin building out your HDX employee experience policy which most likely be the using the defaults in the 19XN releases as the HDX product management team have done an brilliant job working with engineering decreasing the amount of toggles and dials to tweak the HDX protocol and its now these days automatically adapting and adjusting to maintain the human (employee) experience.
1.”Use video codec for compression” then select “Use video codec when preferred“
2. Select “Frames Per Second” use the default which is 30 or increase up to a maximum of 60.
3. Select “Visual quality” set to “High” going beyond this will incur high network bandwidth utilisation, but going beyond this is ok but remember if you are having continual networking performance issues unrelated to Citrix or the HDX offloading capability and employee experience has decreased overall think about a micro change for the current window and then revert. An example of using “Always lossless” is the clinician use case described above.
Tech Insight – Microsoft Teams Optimisation with Citrix
What Supported Hardware Can I Use With Microsoft Teams?
Strongly suggested to only use Microsoft Teams certified headsets, speaker phones, conference phones, cameras e.t.c are listed and available at – https://products.office.com/en-us/microsoft-teams/across-devices/devices. Are my existing Citrix Ready thin clients, headsets, cameras e.t.c using with Skype for Business using Citrix’s HDX Offloading capability compatible? You will need to check with your vendor for there support status with the new optimisation pack for Teams and Microsoft Teams as there have been changes made from both Citrix + Microsoft.
Collection of Suggested Troubleshooting for Microsoft Teams HDX Offloading in CVAD
Understand what Audio & Video (A/V) can be re-direction e.g web camera from supported Operating System (OS) vs. Citrix Workspace app (CWa) – https://www.citrix.com/content/dam/citrix/en_us/documents/data-sheet/citrix-workspace-app-feature-matrix.pdf – Citrix Workspace App (Earlier known as Citrix Receiver) Feature Matrix.
1. The Citrix Support site has a detailed article – https://support.citrix.com/article/CTX253754 which covers off multiple topics for troubleshooting failed HDX optimisations in a CVAD session.
2. How do I know if Teams is Optimised? https://docs.citrix.com/en-us/citrix-virtual-apps-desktops/multimedia/opt-ms-teams.html#enable-optimization-of-microsoft-teams.
3. Troubleshoot MSFT Teams – https://docs.citrix.com/en-us/citrix-virtual-apps-desktops/multimedia/opt-ms-teams.html#troubleshoot.
4. Chromebook – Teams webcam audio problem – https://discussions.citrix.com/topic/408319-chromebook-teams-webcam-audio-problem/#comment-2063142.
The views expressed here are my own and do not necessarily reflect the views of Citrix.